Firewalls have long been considered the first line of defense for computers against cyber attacks but are often considered a hindrance to device usability. Today we’ll explore how firewalls work and how users can optimize firewalls for best security practices.
How Firewalls Work
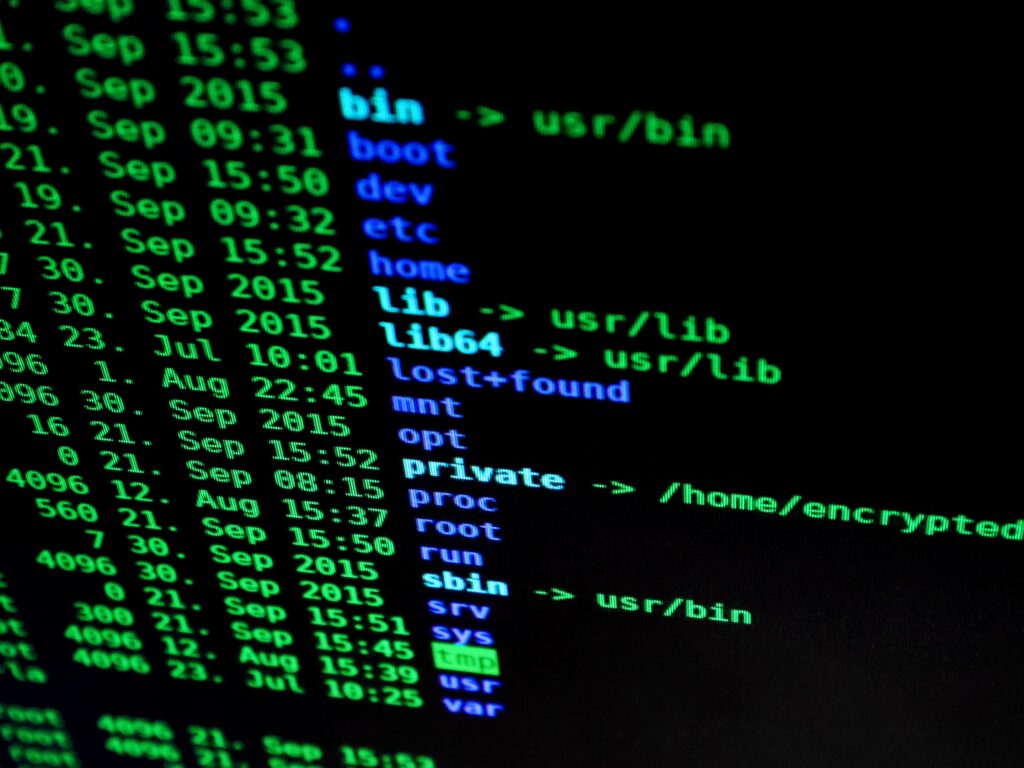
A firewall is a 24/7 shield over your device’s network, filtering through traffic and preventing malicious files enter your system. They inspect all traffic that goes in and out of your network, not only protecting you, but preventing your machine being used to spread malicious code. A hardware firewall, for example, can examine each connection that approaches your machine and determines the location and source that profile of data (data packet) came from.
Most devices come with Proxy and Stateful Inspection firewalls that blocks traffic based on administrator set privileges for what data can pass into/out of that device. Additionally, organizations utilize elastic Cloud Native Firewalls to cover multiple networks at once.
Why You Shouldn’t Disable Your Firewall
Firewalls can be annoying when blocking seemingly secure downloads but one should never disable a defender firewall, especially on a University-owned device. Even if a firewall-blocked application isn’t necessarily malicious, it could still be vulnerable to exploitations and unsecure. If you are certain a software is secure and cannot download it because of a firewall, enable specific ports in order to download it instead of turning off the firewall altogether.
Sources