Spear Phishing
(Photo from – https://oxen.tech/blog/spear-phishing-new-twist-old-scam/)
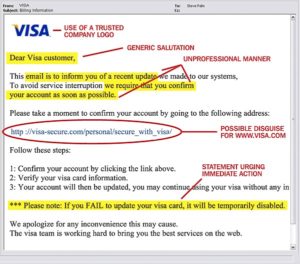
Spear Phishing is really what it sounds like, a directly pointed attack. The attackers gather as much information as they can from the internet to build a more personalized, and believable attack.
(Photo from – http://resources.infosecinstitute.com/category/enterprise/phishing/spear-phishing-and-whaling/#gref)
Whaling
Whaling is a specific form of spear phishing, in which the attacker goes after a high-profile target associated with a business, or government entity. These victims may include but are not limited to senators, CEO’s, and those with access to company’s finances.
- Pay close attention to the emails you receive.
- Look for spelling and grammatical errors. Hover over URLS to reveal the destination of the link. Also hover over the links at the bottom of the email, many times these may look functional but are not.
- If you’re being requested to verify personal information (name, D.O.B, or SSN) don’t use any forms provided in the email. Visit the home page for the business instead and check your account that way, or call customer service for more information when possible.
- Businesses can avoid whale phishing by simply implementing a specific stationary for their emails directed to their employees. Making it easier to spot a spoofed email.
Detailed information regarding passwords and other IT security topics are available on our IT Security website at: SecureIT.Fordham.edu or from our blog at itsecurity.blog.fordham.edu
If you have any questions or concerns, please contact IT Customer Care at (718) 817-3999 or via email to: HelpIT@fordham.edu.