Phishing is the act of attempting to deceive a user into divulging personal or confidential information such as login credentials, credit card information, etc., to gain access to resources that enable them to steal your identity.
Phishing scams usually come in the form of email messages and false websites. Cyber criminals use social engineering to learn about their targets and then use that information to try and gather your personal information.
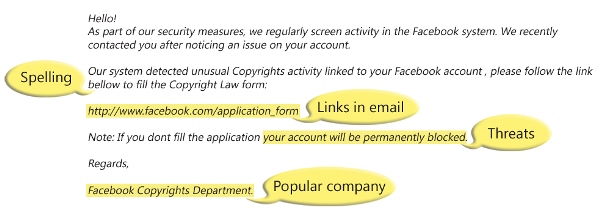
Below is an example of a phishing campaign scam.
Things to look for to identify that you may be targeted include:
- Spelling and bad grammar: Phishing emails are commonly plagued with spelling and grammatical errors.
- Links in emails: Links in emails may appear as though they are taking you to a legitimate website however they can be disguised. Hover over (DO NOT CLICK) links and see if you are being re-routed to some other page.
- Threats: Some emails contain threats to include legal action, time sensitive materials, etc. These are designed to convince you to make a hasty decision and click a malicious link or open a unsafe attachment.
- Spoofing a legitimate website or company: Some emails will appear to come from a legitimate company. However that is far from the case. Again, attackers will try to make everything appear to be legitimate but things such as suspicious URL’s (pages with names not associated with the website or company), or outdated information can be tell-tale signs something is not right.
Visit us daily for more tips tips during National Cyber Security Awareness Month starting October 2nd.
If you believe you are being targeted by a phishing campaign or have received a phishing email, please contact IT Customer Care at (718) 817-3999 or HelpIT@fordham.edu