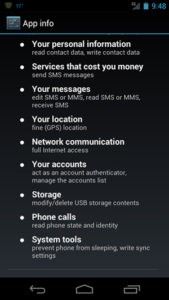
Application permissions on your mobile devices grant an application access to certain information or functions of your phone. When you install an application you are usually greeted with a pop up listing all the permissions the application requests access to. Such permissions include the ability to access your device’s storage and place phone calls. While many simply click through to get the application up and running, it is important to consider what the application is requesting access to and if it is entirely necessary.
If an application is requesting permissions that do not fit the functions of the application (i.e. “find accounts on this device” and “modify your contacts, read your contacts” for an application that only changes your background photo) consider denying the permission to the application. Be cognizant of the applications you download to your device and ensure it is doing only what you intend it to do.
The same principle applies to privacy policies. Though many choose to gloss over them, it is prudent to see how certain information is used, especially in regards to social media sites and applications that require permissions to your information. Make sure you are comfortable with what that information will be used for and how the information is stored.